Leviathan Certificate Authority
What is Certificate Authority?
Certificate Authorities are a critical service in a network.
A Certification or Certificate Authority (CA) creates and issues:
- digital certificates
- public-private key pairs
- Certificate Revocation Lists (CRLs).
Digital certificates issued by the CA are digitally signed which binds the subject name (i.e. Subscriber identity) to the public key.
It’s role is to guarantee that the entity, individual or device granted the certificate is infact who or what they claim to be.
Why do we use a CA?
A CA provides services such as:
- Publication of certificates
- Lists of revoked certificates
- Verification of validity of Certificates.
- Compliant certificates
- Implements certificate profiles
- Maintains the link between the certificate request and the issued certificate
- Checking of revocation information to ensure that the certificate remains trusted and has not been revoked
The CA is a trusted third party that is responsible for physically verifying the legitimacy of the identity of an individual or organisation before issuing the digital certificate.
Functions of a CA
CA’s are vital to security. They perform the following functions.
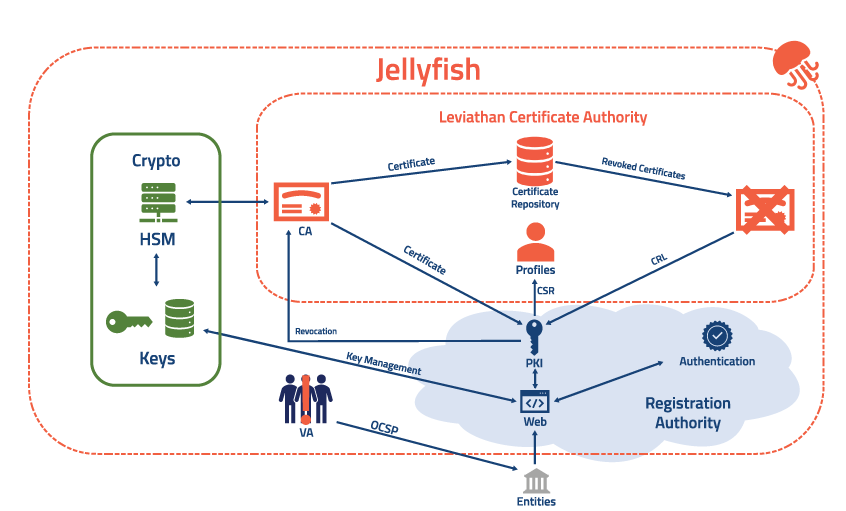
Manages Signing of Certificates

The CA digitally signs the certificate which binds the subject name to the public key. This ensures that the certificates are compliant with the chosen profile before signing any certificate received via the certificate signing request.
Manages the Revocation of Certificates

Manages the revocation of certificates is also available in the Leviathan CA. Information includes the revocation statues and reason. The CA checks the validity of the certificate to ensure it has not been revoked.
Verifies Identity

By implementing certificate profiles, The CA verifies the validity of the certificate by ensuring the verification of requests against profiles before signing.
Issues the Digital Certificate
The Leviathan CA issues and publishes digital certificates.
Generates and Maintains the Certificate Revocation List (CRL)
The CRL ensures all data of all certificate revocations, the reason why and when they were revoked is maintained.
CA Features
Administrator Role
The CA administration role is configured within Jellyfish. The Jellyfish user interface allows user to configure and manage certificate profiles, key management, CRL configuration, configuring allowed algorithms and configuration of workflows for certificate issuance.
Public Key Protection

Protection of public key used to meet CA against undetected modification through use of a digital signature. Each signature is verified upon each access of key.
Data Management

The management of Stored Data is only available to authorised users only. It protects identity, contact information and the evidence of identity information. It restricts the ability of destruction of sensitive data. Leviathan CA also has the ability to store and recover to a previous state at the direction of the administrator.
Profile Enforcement
Leviathan CA implements certificate profiles. Profiles are configurable indirectly via the Jellyfish User Interface.
Private/Secret Key Protection

The protection of the Private/Secret key used for the certificate signing is provided by HSM.
Session Locking Mechanisms

The ability to configure to lock and end a session if the user has been inactive for a configured period of time. It requires the user to re-authenticate to continue using the CA. This mitigates the risk of unattended sessions being hijacked.
Audit Records
The Audit Records log all interactions with the CA by user identity, time, date and action.
The Audit Role can read all information from the logs.
The Audit Records also prevent unauthorised access and protects all data from modification or deletion.
The Audit Records log can be archived for long term retention.






